2026年4月1日再次被入侵
登录时间:东1区05:33
服务商:racknerd
入侵方式:vnc
这次被我抓个正着,看图,哈哈
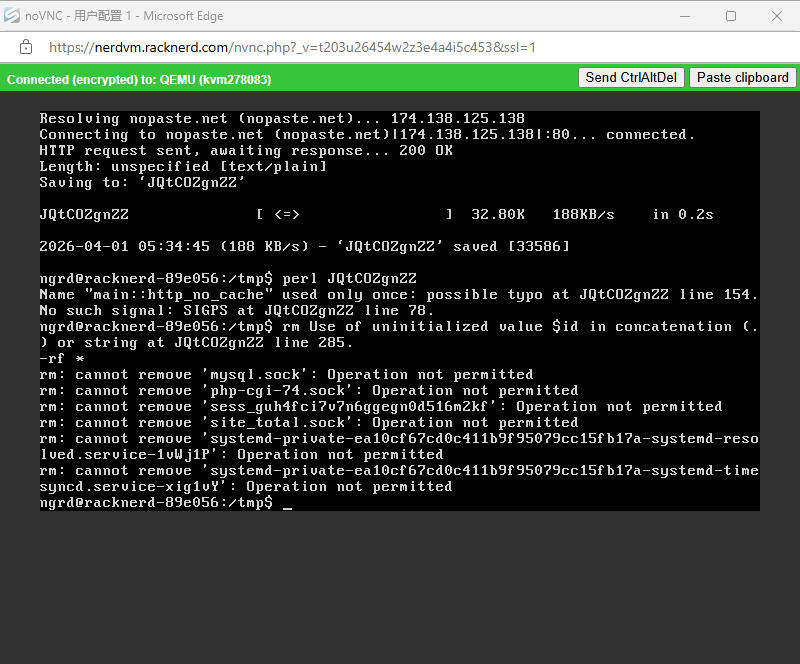
这家伙正在从 nopaste.net 下载一个文件,文件被保存为 JQtC0ZgnZ2,大小约 32.8 KB
尝试用 perl 运行下载的文件,但Perl 脚本有几个问题
执行试图删除 /tmp 目录下的文件,多个文件或套接字(.sock)无法删除,报错 Operation not permitted,权限不足
可能是刚好被我抓入,来不及,哈哈
日志1:
<pre>
login as: root
Authenticating with public key "imported-openssh-key"
Welcome to Ubuntu 18.04 LTS (GNU/Linux 4.15.0-20-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
* Strictly confined Kubernetes makes edge and IoT secure. Learn how MicroK8s
just raised the bar for easy, resilient and secure K8s cluster deployment.
https://ubuntu.com/engage/secure-kubernetes-at-the-edge
* Canonical Livepatch is available for installation.
- Reduce system reboots and improve kernel security. Activate at:
https://ubuntu.com/livepatch
Last login: Wed Apr 1 01:30:43 2026 from
root@racknerd-89e056:~# top
top - 05:40:43 up 8 min, 2 users, load average: 1.09, 0.85, 0.43
Tasks: 106 total, 2 running, 77 sleeping, 0 stopped, 0 zombie
%Cpu(s): 67.9 us, 32.1 sy, 0.0 ni, 0.0 id, 0.0 wa, 0.0 hi, 0.0 si, 0.0 st
PID USER PR NI VIRT RES SHR S %CPU %MEM TIME+ COMMAND
2467 ngrd 20 0 33692 7492 3740 R 98.0 0.7 5:40.34 /usr/sbin/s+
178 root 20 0 0 0 0 S 0.3 0.0 0:00.05 jbd2/vda1-8
586 root 20 0 1687224 11996 10168 S 0.3 1.2 0:00.22 site_total
597 root 20 0 695912 23036 9868 S 0.3 2.3 0:02.70 fail2ban-se+
1621 mysql 20 0 892232 279944 16604 S 0.3 27.7 0:02.50 mysqld
2700 root 20 0 41980 3952 3364 R 0.3 0.4 0:00.11 top
1 root 20 0 77304 8440 6628 S 0.0 0.8 0:01.46 systemd
2 root 20 0 0 0 0 S 0.0 0.0 0:00.00 kthreadd
3 root 20 0 0 0 0 I 0.0 0.0 0:00.00 kworker/0:0
4 root 0 -20 0 0 0 I 0.0 0.0 0:00.00 kworker/0:0H
6 root 0 -20 0 0 0 I 0.0 0.0 0:00.00 mm_percpu_wq
7 root 20 0 0 0 0 S 0.0 0.0 0:00.28 ksoftirqd/0
8 root 20 0 0 0 0 I 0.0 0.0 0:00.34 rcu_sched
9 root 20 0 0 0 0 I 0.0 0.0 0:00.00 rcu_bh
10 root rt 0 0 0 0 S 0.0 0.0 0:00.00 migration/0
11 root rt 0 0 0 0 S 0.0 0.0 0:00.00 watchdog/0
12 root 20 0 0 0 0 S 0.0 0.0 0:00.00 cpuhp/0
</pre>
被创建了一个ngrd账户,植入了恶意程序
这家伙绝对是我服务器的常客,我重装系统都还没有几天就被搞了,真是神仙,哈哈。
前几天我以为是火车头采集器的问题,现在看来可能不是,但是不排除有这个嫌疑,你就说巧不巧吧,嘿嘿
我现在重新安装系统,并把所有网站设置了basic auth,配合fail2ban的filder和acion屏蔽所有攻击ip
然后禁用控制台登录(永久),至于ssh入口是没可能的进的去的。
看看这位神仙要花多久!~